Employees using insecure devices and networks have created new security vulnerabilities for businesses – and with Google tallying more than 18 million malware and phishing emails related to COVID-19 each day earlier this year, hackers have never been more active.
Accenture’s latest State of Cybersecurity Report found that the current average cost per attack for businesses is $380,000 per incident. IBM’s Cost of a Data Breach report places the full global costs of a breach at ten times that – $3.86 million. Regardless of the size of your business, these kinds of costs can be devastating. The IBM report also found that 76% of those surveyed expected that remote work would “increase the time to identify and contain a breach”.
How to spot a cyber scam - download free toolkit!
With the uncertainty of Covid-19 to business operations – is your business critical data secure? Would you know how to protect your business from cyber attacks or what to do in the event of a data breach? Or do you now find yourself without a secure digital environment when you need it most?
Download our free security toolkit and discover 5 areas where you can make some quick changes to get your IT working for you.
Making sure your business is prepared for the latest security risks is therefore crucial to survival. Here are our top tips to help you navigate the new challenges of cybersecurity:
Move to Zero Trust architecture Traditionally, organizations have followed a ‘castle-and-moat’ approach, assuming that if you protect your operations then everything else will follow. But if your workforce is no longer centralized, people’s defences become ever more important.
The Zero Trust principle is a security methodology that is centered on the assumption that no person or device within or outside of a network can automatically be trusted. It is a holistic approach to network security that entails a wide range of technologies and assets, and users and devices must be authenticated and authorized to access multiple, smaller perimeters to access data.
Once trust has been initially established, the architecture is maintained through a combination of protocols including multi-factor authentication, privileged access, and real-time monitoring.
Protect your enterprise and customers with a remote working layered defense strategy With a distributed workforce, the number of endpoints to protect increases dramatically – and you’d be right in thinking that extending your corporate network to people’s homes with VPNs, SSLs and remote system monitoring is your first step to staying protected.
However, if you are trying to prevent financial loss and improve the overall value of your network, then layering your security protocols is your best holistic line of defense. It will reduce the false positives that prevent your company from maintaining interaction with legitimate contacts, while at the same time helping you improve your visibility.
By establishing a verified pathway that goes from the network to the server following a defined set of points that lie in between, threats are detected quicker and easier, and eliminated without slowing down your system’s operation. The layered security concept creates an interwoven network of protection that prevents unwanted intruders from accessing (or even lingering for long periods of time) within your system.
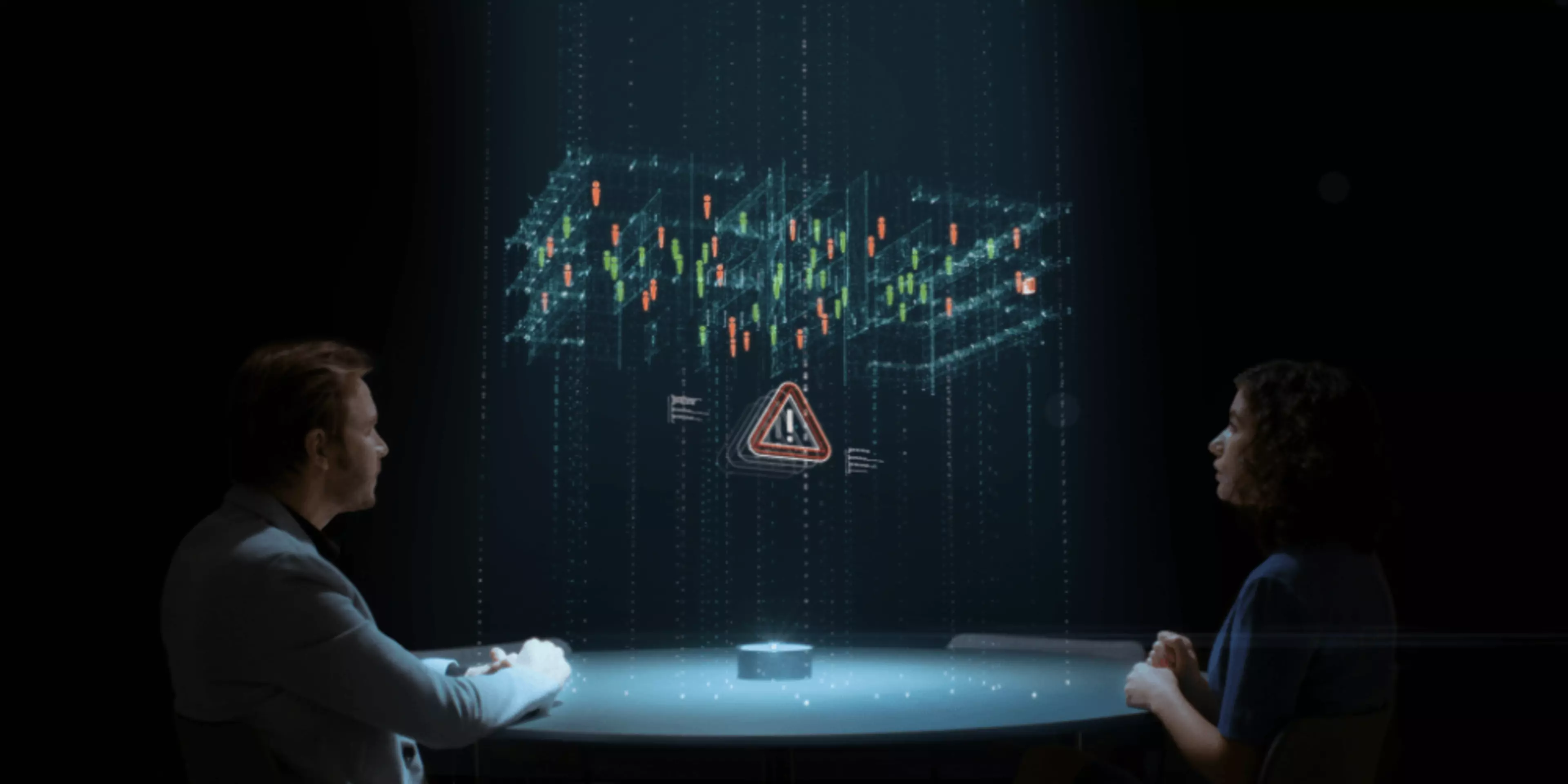
Focus on dynamic security & real-time actions If there’s one prevalent trend we should all be aware of, it’s the demand for everything in real-time – whether it’s our takeout, Amazon Prime deliveries or internet speed. The same applies to cybersecurity, and even more so when you don’t have one control base.
Our recommendation is to adopt a philosophy of constant governance and agility, which continuously assesses different attack vectors. This means understanding how hackers and adversaries can leverage a weakness to penetrate your network and infrastructure to assess confidential data. Using data to your advantage, you can build better threat intelligence that anticipates threats before they become harmful.
To support building this dynamic risk profile, organizations should also look to deploy an outside-in cybersecurity approach. This means searching through the internet, social media, even hackers’ communities to understand what intellectual property, financial records, personal data and other types of assets are easily accessible.
And of course, your cybersecurity strategy should be a live document and reviewed at least monthly, if not more often, to check what new external threats may need preparing for.
Rethinking the future of security
At Konica Minolta, we’re here to support you with these vital steps on your security transformation journey. If you’d like more information visit us: